SQL Server Audit: Best Practices
Summary: Auditing the SQL Server database is a complicated, multi-faceted process. This article explains how to conduct security, server, and database performance audits.

SQL Server is a powerful database management system that ranks first among the most popular databases in the world. It highlights the many modern features that keep the database secure and meet top industry standards. In today's world, more sensitive and confidential data is stored in databases, so ensuring their security and compliance is crucial.
Understanding SQL Server Audit
Database audits are critical parts of compliance and security audits aimed at protecting corporate data. They help identify potential weaknesses, security risks, and performance issues.
SQL Server auditing is based on three pillars: security audit, server audit, and database performance audit. This article contains examples from a specific SQL Server audit to demonstrate real-life pain points and options to correct them.

Best Practices for SQL Server Auditing
Let's review the best practices for making SQL Server Audit a breeze:
- Define the goal and the scope of your audit. While creating a database audit specification, it is essential to clearly state the goal and define the audit scope. Clearly defining the reasons for the audit can reduce the need for further modifications later. The goal is to specify whether the whole database engine needs to be audited or specific server instances.
- Review the data regularly. Do not wait for a disaster to come. It is advisable to audit the data at least once a week. This approach helps you find any activities that break the security policy. You can address them quickly and prevent possible threats.
- Determine audit roles. Auditors are generally responsible for auditing logs to identify potential breaches. At the same time, database administrators play an important role. They ensure that all necessary auditing systems are in place and work well.
- Review the integrity of the audit. Monitor the SQL Server audit process. This helps ensure that no unauthorized changes happen. Some users may turn off auditing before doing illegal actions.
- Follow the principle of least privilege. Remember to limit access to specific data only to the users who need it.
Schedule a call with the Ispirer experts to discuss the database audit
Security Audit of Microsoft SQL Server
Databases are the backbone of any organization and store large quantities of data. The variety of data stored in databases depends on where a company operates. Any database stores sensitive and personal data regardless of the company's business scope.
Organizations must protect valuable assets like customer information, financial transactions, and production processes. Taking the proper steps to prevent unauthorized access to this information is essential.
A data breach could have serious consequences, including identity theft, financial fraud, and other threats. It can also harm the company's reputation. It may lead to legal issues and fines for breaking data protection laws.
Regular vulnerability and threat SQL Server audits can help ensure high database resistance to security breaches. A database audit specification has no room for a mess. Proper database configuration, auditing events, and database-level permissions are essential to auditing the database properly. Let's examine each point in more detail.
Analyze SQL Server security settings
First, verify that the SQL Server is running the latest security patches and updates. They are crucial for maintaining database security because they address newly discovered vulnerabilities and weaknesses in the software.
Cybercriminals are always looking for new ways to exploit these flaws. They want to access databases without permission and steal private data. Organizations can avoid these threats by regularly updating and patching the database software and protecting their information from potential breaches.
Second, ensure your company adheres to a strong and secure password policy. A password is the first line of defense against unwanted access. It must be strong to keep the database secure. Even with many tips to create strong passwords, many employees still make them easy to guess, putting the database at risk of a breach.
Database administrators should enforce a firm password policy. They must require users to create strong passwords that meet specific complexity rules. Using this method can help prevent weak passwords and reduce the risk of unauthorized access to the database.
Disable or remove unnecessary logins
The final step in security settings analysis is to disable or remove any unnecessary logins, users, or roles to prevent unauthorized access to sensitive files. How do you do that?
- Review the server and database-level permissions. To begin with, analyze all the permissions to verify that they are correct. This includes granting appropriate permissions to users, roles, and groups and ensuring that no user has unnecessary permissions. Also, check for redundant permissions and remove them to reduce the risk of third-party access.
- Enable SQL Server auditing and monitoring. This is important for tracking key security events, including successful and failed login attempts.
They also cover changes to server and database objects, modifications of user permissions, and access to sensitive data. Tracking these events can help detect suspicious activity, identify potential vulnerabilities, and prevent unauthorized access.
Many regulations and standards, like HIPAA, PCI DSS, and GDPR, require companies to track access to sensitive files and report any unauthorized access or data breaches. Event monitoring can help organizations meet regulatory requirements and best industry standards.
When analyzing DB user privileges, we often discover a plethora of problems. For example, in our practice, we found cases where almost all users had the rights of db_owner.
Such an approach does not comply with any generally accepted database security policies. Only one user should have db_owner rights. It is critically important since any of these users has the right to unlimited access to the database up to its removal.
We also found that some of the users with db_owner privileges also had personal privileges. Don't give users personal privileges. They weaken database protection against unauthorized access and changes to data and structure.
Schedule a call with the Ispirer experts to discuss the database audit
Server Audit
Audits are essential for ensuring that servers are secure, optimized, and configured according to best industry practices. But before we can begin inspecting the database server, we should understand what a server-level audit is.
To create a server audit specification, you should thoroughly examine the policy, procedures, and resources allocated to a server. This review includes server activities such as user logins, system changes, file access auditing, and important events. The main goal of a server audit is to ensure that the server is secure, compliant, and performing at its best.
System administrators analyze server audit logs to find security vulnerabilities, fix issues, and ensure the server meets industry compliance requirements. Database admins can also carefully check server logs to discover and fix unauthorized access attempts or suspicious activities.
By conducting a server audit, you can identify and address any potential issues before they cause significant problems. A server audit involves a comprehensive review of server configurations, network review, and resource allocation.
Server Configuration Review
The server configuration review ensures the server has the latest security patches and updates. It helps to ensure that the server is better equipped to mitigate attacks and is less vulnerable to security breaches.
Moreover, you must configure SSL encryption to ensure the information is encrypted when transmitted. Enabling strong password policies helps to ensure that passwords are complex and changed regularly. Lastly, turning off unnecessary services or features reduces the attack surface, making the server more secure.
Network review
Checking the network segment that lets users access the server is essential because of the changing threat landscape. Criminals create new ways to attack online, so organizations must regularly check their networks to stay safe.
A network audit involves examining security measures used to protect the network. These measures include firewalls, intrusion detection systems, access controls, and other security protocols. Checking wireless network security is crucial. Encryption and authentication methods must be strong to prevent unauthorized access to database information or important files.
Alongside the security measures, reviewing network policy and procedures is a crucial aspect of a network audit. It involves checking the access controls, password policies, and network segmentation to ensure they are effective and being followed.
Poorly optimized networks can also impact the database's performance and stability, leading to slow query execution times, increased downtime, and reduced productivity.
The first step in analyzing the network is to identify all the network components connected to the server. All network devices, including switches, routers, firewalls, load balancers, and others, fall into this category. Next, review the network topology to understand how data flows through the network and identify potential vulnerabilities or bottlenecks.

Resource Allocation Review
Efficient server operation depends on proper resource allocation. In this regard, we highly recommend monitoring server performance to identify any bottlenecks or performance issues. Monitoring disk I/O, memory usage, and CPU utilization ensures no resource contention. It is also extremely important to analyze the server hardware specifications to ensure they match the workload.
Here is an example of the RAM load level measured during the SQL Server audit.
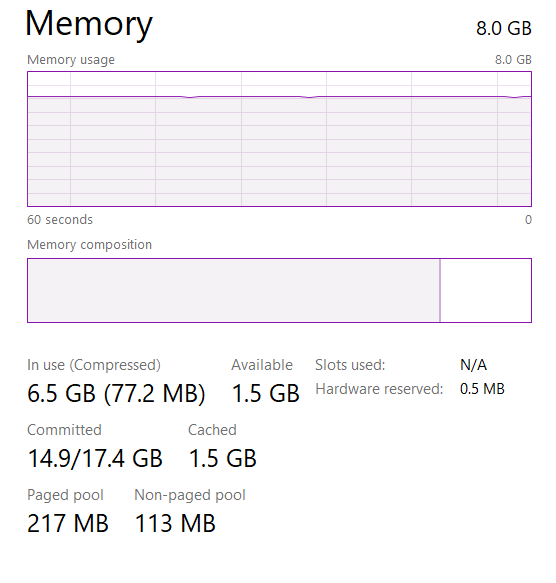
The RAM load was okay (around 80%) throughout the observation time, as seen in the screenshot. However, during server overloads, operational memory can be in short supply. To eliminate possible trouble, we recommend increasing the amount of RAM by 40-50%. This will provide a 50% RAM reserve, which is a generally accepted recommendation for smooth database operation.
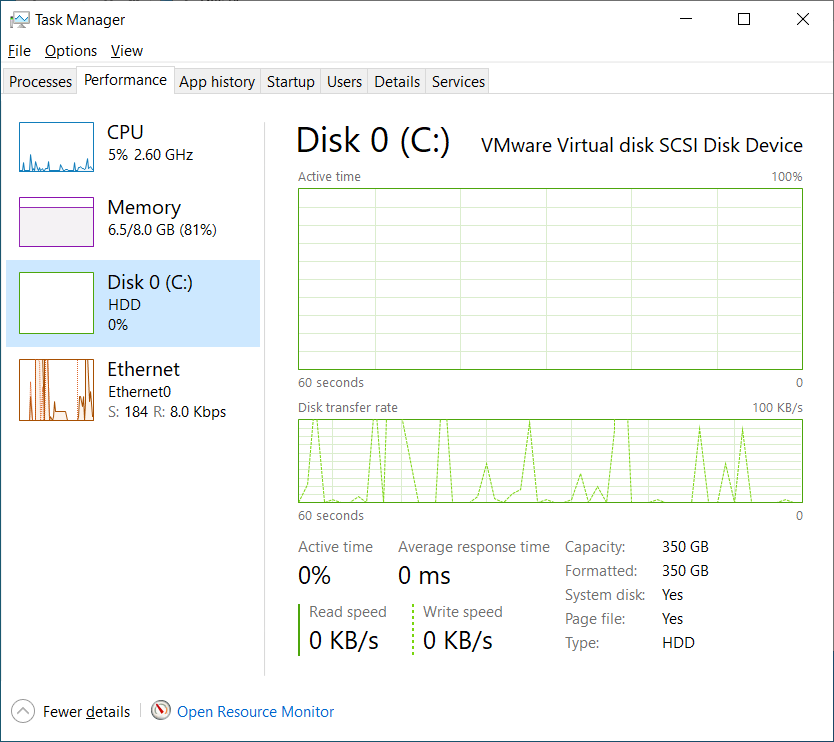
It is worth paying attention to the amount of free space on the hard disk. The amount of free space on your hard disk can affect the server's overall stability and reliability. During SQL Server auditing, we can sometimes observe that the hard disk has very little space left, which can cause concern under heavy load and when performing multiple write operations. Free space is highly recommended to be added to the disc where the database is stored.
Database Audit
One key reason why database audit should be at the center of your attention is optimization. When a database is optimized, it performs faster and more efficiently. It improves the user experience and enables organizations to handle larger volumes of information and scale their operations more effectively.
Database performance audits can help identify issues with database design or configuration affecting performance. SQL Server audit specification involves reviewing the schema, tables, indexes, and other database objects to ensure they are optimized for performance and scalability.
Indexes allow a database to locate data and speed up query execution quickly. Therefore, it is essential to ensure that indexes are optimized for the workload and do not cause performance issues.
Query execution is another significant issue that can impact database performance. It involves analyzing the execution plans of database queries to identify performance issues such as slow-running queries, missing indexes, or inefficient queries. By identifying these problems, you can optimize the query execution speed and bring the overall database performance to a new level.
Let's refer to our example database. The graph below shows the statistics of accesses to tables (all queries, including the execution of business logic objects).
The chart contains the top candidate tables for memory optimization based on the database workload's access patterns. The horizontal axis represents the decreasing effort of memory optimization, while the vertical axis represents the increasing benefits of memory optimization in a company’s workload. The tables at the top right corner should be prioritized first for memory optimization.
The graph clearly shows that optimizing the menuclassitemstable and domain_values tables is necessary. Updating and reorganizing the indexes is imperative. Additionally, adding partitions to speed up work would make sense. It may also be worth looking at other tables in the graph. Reorganizing these tables will significantly improve performance, as most calls are made to these tables.
Conclusion
You can audit SQL Server databases or hire our team for professional database audit services. The Ispirer team's extensive experience ensures top-notch auditing services and high-quality database analysis.
If you are looking for an efficient way to audit your SQL Server database, the Ispirer team is the best option. Book a call with the Ispirer expert to discuss all your questions regarding your database audit.

